The Number That Changes How You Think About This
73% of Indian cybersecurity professionals who join global teams are hired through referral networks, not job boards. I’ve watched companies spend 4–6 months on sourcing cycles for roles that our network fills in 3–4 weeks — because they started with the wrong channels.
This isn’t a talent shortage story. India graduates over 60,000 cybersecurity professionals annually. The shortage is a hiring methodology problem. In fact, the market reality is even more nuanced — India faces a shortage of over 320,000 cybersecurity professionals in 2026, despite having one of the fastest-growing security talent pools globally. The gap isn’t about absolute numbers; it’s about access to the right talent at the right time through the right channels.
When Supersourcing was building the security compliance layer for Open Money’s banking and settlement platform — a system handling real-time transactions across 40+ banking partners — we needed penetration testers, SOC analysts, and a cloud security architect who understood RBI’s regulatory framework. We didn’t post on LinkedIn. We activated a sourcing model built specifically for specialized security talent.
What I’m going to share here is what actually works when you need to hire cybersecurity experts in India. Not the sanitized version. The one with the numbers, the mistakes, and the parts that most vendors won’t tell you upfront.
Why India for Cybersecurity? The Actual Answer
Hire cybersecurity experts in India and you get access to one of the world’s fastest-growing security talent ecosystems — but the framing of “cost savings” undersells what’s really happening here.
India’s cybersecurity workforce has compounded at 22% annually over the last six years. The country now hosts the regional security operations centers for 6 of the top 10 global banks. Major compliance certifications — CISM, CISSP, CEH, OSCP — have seen Indian examination volumes grow by 340% in the last four years. NASSCOM’s latest talent report puts active certified cybersecurity professionals in India at 2.1 million, with 400,000 specializing in cloud security and application security.
That’s not a coincidence. It’s the result of India’s IT services industry forcing its talent up the value chain.
What this means practically: when you hire a senior threat analyst or red team engineer from India with 6–8 years of experience, you’re typically hiring someone who has worked across 3–4 different industry verticals, has exposure to multi-cloud security architectures, and has dealt with compliance regimes from GDPR to SOC 2 to ISO 27001. That cross-sector depth is genuinely rare in single-market talent pools.
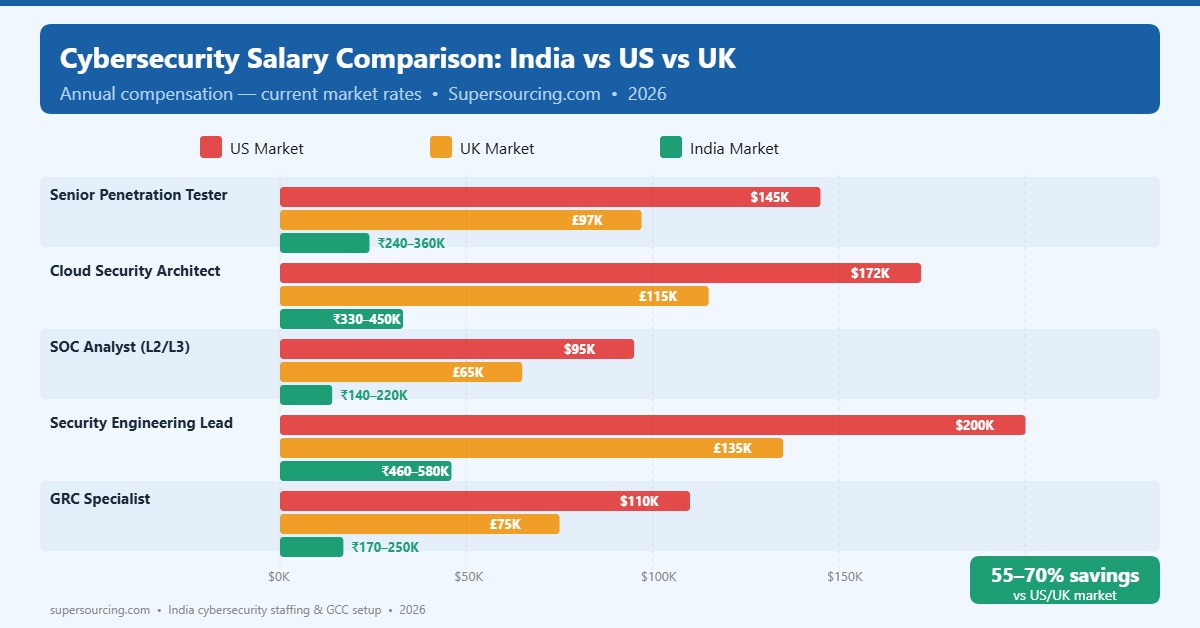
| Role | US Market (Annual) | UK Market (Annual) | India Market (Annual) |
| Senior Penetration Tester | $130,000–$160,000 | £85,000–£110,000 | ₹18–28 lakhs ($21,000–$34,000) |
| Cloud Security Architect | $155,000–$190,000 | £100,000–£130,000 | ₹25–40 lakhs ($30,000–$48,000) |
| SOC Analyst (L2/L3) | $80,000–$110,000 | £55,000–£75,000 | ₹10–18 lakhs ($12,000–$22,000) |
| Security Engineering Lead | $180,000–$220,000 | £120,000–£150,000 | ₹35–55 lakhs ($42,000–$66,000) |
| GRC Specialist | $95,000–$125,000 | £65,000–£85,000 | ₹12–22 lakhs ($14,000–$26,000) |
These are current compensation numbers, not the arbitrage-era figures from half a decade ago. The savings are still substantial — typically 55–70% depending on seniority and specialization — but the more interesting story is that you’re not trading quality for cost. You’re accessing the same certification frameworks and often the same enterprise environments at significantly lower all-in costs.
What “Hire Cybersecurity Experts India” Actually Means Across Role Types
There’s no such thing as a generic cybersecurity expert. When clients come to Supersourcing asking to “hire a cybersecurity person,” the first 20 minutes of any conversation is clarifying exactly what problem they’re trying to solve.
Here’s how the landscape actually breaks down:
Offensive Security (Red Team / Penetration Testing)
These are the professionals conducting ethical hacking, vulnerability assessments, and simulated breach scenarios. In India, the best offensive security talent is concentrated around Pune, Bangalore, and Hyderabad — cities with active CTF communities and bug bounty ecosystems. Certifications to look for: OSCP, GPEN, CEH (advanced track). These professionals typically come from product security backgrounds at large Indian IT services firms or fintech companies.
Defensive Security (Blue Team / SOC)
Security Operations Center analysts — incident response, threat detection, SIEM management, threat intelligence. India has one of the world’s largest SOC workforces, partly because 24/7 coverage is operationally easier to staff across time zones. L2/L3 analysts with SIEM expertise (Splunk, Microsoft Sentinel, IBM QRadar) and SOAR experience are available at scale. Average experience profile for strong L3 hire: 5–7 years, 2–3 major incident response engagements.
Cloud Security Engineering
The fastest-growing segment. Professionals who design and implement security controls in AWS, Azure, and GCP environments — IAM architecture, network security groups, data encryption, secrets management, CSPM implementation. The India cloud security talent pool has expanded significantly as AWS, Microsoft, and Google have built major centers in Hyderabad and Bangalore. CCSP, AWS Security Specialty, and Google Professional Cloud Security Engineer are the certifications to validate here.
Application Security (AppSec)
Security engineers embedded in development pipelines — SAST/DAST tooling, secure code review, threat modeling, DevSecOps practices. When the Supersourcing team helped Brillio scale its enterprise digital transformation practice, AppSec engineers were the hardest roles to fill — not because of supply, but because truly good AppSec talent requires both security depth and software development credibility. Expect longer hiring timelines (6–8 weeks vs. 3–4 weeks for other roles) and higher compensation premiums.
GRC (Governance, Risk, Compliance)
India has deep bench strength in compliance-oriented security roles — ISO 27001 lead implementers, SOC 2 auditors, GDPR/data privacy specialists, RBI regulatory compliance specialists. Particularly relevant if you’re building a GCC in India or if your product serves regulated industries.
Security Architecture
Senior-most category — professionals who design enterprise security frameworks, define security policy, evaluate zero-trust architectures, and own the security technology roadmap. These roles are scarce everywhere, including India. Realistic hiring timeline: 8–12 weeks for the right profile.
 The Three Hiring Models — What Each Actually Costs
The Three Hiring Models — What Each Actually Costs
When you decide to hire cybersecurity experts in India, you’re choosing between three fundamentally different operating models. Most articles present these neutrally. I’ll tell you what I actually see when clients choose each one.
Model 1: Direct Hire (Permanent Employment)
You hire the professional directly as an employee of your Indian entity or a Professional Employer Organization (PEO). The professional is exclusively yours, full-time.
Works best when: You have a long-term roadmap (18+ months), need cultural integration into your product team, or are building a GCC security function.
Real costs:
- Recruitment: 15–25% of annual CTC (if using an agency) or 8–12 weeks of internal sourcing effort
- Employer costs in India: add 20–25% on top of CTC for PF, gratuity, health insurance, professional tax
- Onboarding and ramp: 4–8 weeks before full productivity
- Total first-year cost: 1.4–1.5x stated CTC
What most people miss: India’s employment market for senior security talent is candidate-driven. If your offer process takes more than 3 weeks from first interview to offer letter, you will lose candidates. I see this happen repeatedly with companies that have multi-stage approval processes.
Model 2: Staff Augmentation (Contract)
You engage security professionals through a staffing partner who handles employment, compliance, and payroll. The professional works on your projects, integrated into your team.
Works best when: You need to scale quickly, have variable workloads, or want to test a role before committing to a permanent hire.
Real costs:
- Monthly billing rates: typically 1.3–1.6x the professional’s monthly take-home, depending on seniority and specialization
- No recruitment fee, no employer overhead
- Notice periods: typically 2–4 weeks
- Flexibility premium: 15–20% higher per-hour cost than equivalent direct hire
What most people miss: The best security professionals in India often prefer permanent employment with strong career paths over contract arrangements. Staff augmentation works well for L1–L3 SOC roles and penetration testers; it’s harder to attract top-tier security architects on a contract basis.
Model 3: Dedicated Security Team (Managed Team)
A fully managed security team — hired, onboarded, and operated by a partner like Supersourcing — working exclusively on your security functions. Team lead is accountable to you; partner handles HR, infrastructure, and compliance.
Works best when: You don’t have the internal capability to manage a distributed security team, need a complete security function fast, or are building a managed security services offering.
Real costs:
- Fully loaded monthly cost: typically ₹8–15 lakhs per person depending on seniority mix
- Team lead premium: 20–30% higher than individual contributor rates
- Setup timeline: 6–10 weeks for a complete team of 4–8 professionals
- Management overhead on your side: low (3–5 hours/week for team lead sync)
Where Companies Go Wrong When Hiring Cybersecurity Talent in India
I’ve been part of enough hiring processes — both successful and broken — to see the patterns clearly. Most mistakes fall into four categories.
Mistake 1: Certifications as a proxy for competence
CISSP and CISM are knowledge certifications. They test whether someone can pass an exam. They do not test whether someone can design a zero-trust architecture for your specific cloud environment or lead an incident response under pressure.
I’ve interviewed CISSP holders who couldn’t articulate the difference between a SIEM rule and a threat intelligence feed. I’ve also worked with engineers without a single certification who built genuinely robust security programs.
Certifications are a starting filter, not an evaluation framework. The actual evaluation framework is: practical skills assessment, architecture problem walkthrough, and at least one simulated scenario relevant to your environment.
Mistake 2: Hiring for current threats instead of adaptive capability
The threat landscape today looks different from three years ago. LLM-assisted phishing, AI-generated malware, and supply chain attacks have changed the offensive toolkit significantly. If you’re evaluating candidates on their knowledge of attacks from 3 years ago, you’re hiring for yesterday’s environment.
What actually matters: Does the candidate demonstrate continuous learning? Are they active in security communities (CTFs, bug bounties, security research)? Can they reason about novel scenarios they haven’t seen before?
Mistake 3: Underestimating cultural integration time for distributed security teams
Security functions require high trust and fast communication. When you hire cybersecurity experts in India for a distributed team, the communication infrastructure matters as much as the technical capability. Teams that succeed have: clear escalation paths, overlap hours with their US/EU counterparts (typically 2–3 hours minimum), and explicit protocols for incident response handoffs.
Teams that struggle have distributed security professionals who are technically strong but effectively siloed because the communication architecture wasn’t built.
Mistake 4: Single-threaded sourcing
The best cybersecurity talent in India is not primarily sourced through LinkedIn or Naukri. They’re sourced through:
- Security community networks (null community chapters in major cities, ClubHack, c0c0n)
- Bug bounty program alumni networks
- CTF competition alumni
- Direct referrals from professionals already in your network
- Specialized security staffing partners with active community relationships
Supersourcing’s AI-powered hiring platform maintains active relationships with 12,000+ security professionals across India. That bench allows us to move in 3–4 weeks on roles that would take 8–12 weeks through conventional sourcing. It’s not magic — it’s relationship infrastructure built over years.
 What a Real Security Hiring Process Looks Like (Week by Week)
What a Real Security Hiring Process Looks Like (Week by Week)
When Supersourcing worked with Pennywise on their digital transformation program, they needed a full security team — cloud security engineer, AppSec specialist, and GRC lead — to stand up within 10 weeks. This is how a disciplined process actually runs:
Weeks 1–2: Role Definition and Sourcing Brief
Most JDs for security roles are terrible. They’re either too generic (“5+ years in cybersecurity”) or copy-pasted certification lists that don’t reflect the actual work. A good sourcing brief specifies: the technologies in your stack, the compliance frameworks you need to operate within, the key problems the hire will solve in the first 6 months, and the team structure they’ll work within. Getting this right saves 2–3 weeks of irrelevant candidate volume.
Weeks 3–5: Candidate Pipeline and Initial Screening
For senior security roles, expect to review 30–45 profiles to produce 8–10 who merit a technical screen. Screening at this stage is skills-based: practical assessment on a security scenario relevant to your environment. Not a quiz. A real problem.
Weeks 5–7: Technical Interviews and Architecture Walkthrough
Two rounds: a deep-dive technical interview with your senior security team, and an architecture/case study session. The case study should give the candidate 24–48 hours to think through a scenario and present their approach. How they reason matters as much as what they conclude.
Weeks 7–8: Reference Checks and Offer
Security professionals warrant thorough reference checks — not just “was this person a good employee” but “how did they behave under pressure, how did they communicate risk to non-technical stakeholders, what was their approach to ethical dilemmas.” These conversations take time. Budget for them.
Weeks 8–10: Onboarding
Background verification (criminal record, credential verification, previous employment) is non-negotiable for security hires and takes 2–3 weeks in India. Security clearance for sensitive environments adds another 2–4 weeks. Do not skip these steps.
The GCC Security Team Setup: What’s Different
Global Capability Centers are increasingly choosing India not just for cost optimization but for building genuine security competency. When a company sets up a GCC security function in India, the hiring challenge is different from project-based staff augmentation.
A GCC security team needs:
- Leadership that can operate autonomously, not just execute instructions
- Professionals with strong English communication skills for working with global stakeholders
- Understanding of the parent organization’s industry regulatory environment
- A career path that retains talent beyond 2–3 years (the typical attrition point)
The cities matter. Bangalore and Hyderabad have the deepest enterprise security talent pools. Pune is strong for application security. Chennai has a growing compliance and GRC talent base. Gurgaon and Noida attract talent for organizations with large US corporate connections.
When Supersourcing helped set up GCC security functions, the pattern that works is: hire the security lead first (12–16 week process for the right person), then build the team around their network and hiring preferences. A good security lead in India will bring 3–5 strong recommendations within their first 30 days. That’s not a nice-to-have. It’s how the best teams get built.
Compliance and Legal Considerations Nobody Mentions
Hiring cybersecurity professionals in India involves compliance obligations that are easy to underestimate.
- Data protection: India’s Digital Personal Data Protection Act (DPDPA), enacted in 2023, imposes obligations on how personal data is processed. If your Indian security team has access to European or US user data (which SOC analysts typically do), you need data processing agreements, data transfer mechanisms, and clearly defined data handling protocols in employment contracts.
- Background verification: Standard background checks in India cover criminal history, educational credentials, and previous employment. For security-cleared roles or those with access to sensitive data, additional checks — social media screening, financial background, credit history — are increasingly standard. Plan for 3–4 weeks; do not bring security professionals live in your environment before verification is complete.
- IP and NDA considerations: India’s IT Act provides reasonable IP protections, but employment agreements should explicitly cover source code ownership, security research conducted on company time, and handling of vulnerability disclosures. This is particularly important for red team and AppSec roles.
- Export control: For certain security technologies (encryption tools, penetration testing frameworks), US and EU export control regulations may affect what your Indian team can access and use. This requires a compliance review before you set up the team, not after.
What Good Looks Like: Evaluating a Cybersecurity Hiring Partner in India
If you’re using a partner to hire cybersecurity experts in India, evaluate them on five criteria that most companies don’t ask about:
- Community depth, not just database size
Anyone can license a resume database. What matters is whether the firm has genuine relationships in the security community — sponsoring security conferences, participating in CTF events, having security professionals refer candidates. Ask them to name the security communities they’re active in.
- Technical evaluation capability
Can the hiring partner actually evaluate security candidates, or are they pattern-matching on keywords? Supersourcing uses domain-expert technical reviewers for security roles — professionals who can distinguish a genuinely capable threat analyst from someone who has memorized OWASP Top 10.
- Retention track record
A 12-month retention rate below 75% is a red flag. High early attrition in security hires almost always traces back to role misrepresentation at the sourcing stage — the professional was sold on a role that didn’t match reality. Ask for retention numbers at 6 months and 12 months.
- Compliance infrastructure
Can the partner handle employment compliance (PF, ESI, professional tax, gratuity), background verification, and DPDPA-compliant employment agreements? Or will you need to manage these separately?
- GCC experience
If you’re building a long-term security function, has the partner done this before? What does their GCC setup process look like? What’s the typical timeline?
 What Most People Get Wrong About Indian Cybersecurity Salaries
What Most People Get Wrong About Indian Cybersecurity Salaries
The compensation data you find in generic salary surveys is almost always wrong for two reasons: it lags reality by 12–18 months, and it averages across cities and experience levels in ways that obscure the ranges that actually matter.
A few realities playing out right now:
Senior cloud security architects in Bangalore with AWS/Azure Security Specialty certifications and 8+ years of experience are receiving 35–55 lakh CTC offers. The floor has risen 40% over the last five years. If you’re benchmarking against old survey data, you’re going to lose candidates at the offer stage.
Penetration testers with OSCP certifications and active bug bounty track records command a 20–30% premium over the certification-only market rate. The bug bounty portfolio is a verified performance credential that the market has started pricing in.
Security professionals who have worked in regulated industries — banking, insurance, healthcare — command a 15–25% premium over equivalent experience in less regulated sectors. If you’re a fintech or healthtech company, this premium is worth paying.
The biggest salary trap: hiring at the bottom of the market to “save money” on security roles. The risk-adjusted cost of a mediocre security hire is not worth the ₹5–10 lakh annual savings. I’ve seen this calculus play out badly too many times.
Frequently Asked Questions
1. How long does it take to hire a senior cybersecurity expert in India?
For senior roles (6+ years experience), plan for 8–12 weeks from sourcing briefs to offer acceptance. Specialized roles — cloud security architect, red team lead, security engineering lead — can take 12–16 weeks if you’re sourcing through conventional channels. With a specialized security hiring partner and an established talent network, this compresses to 4–6 weeks for most senior roles. Background verification adds 2–3 weeks post-offer before the professional can access sensitive systems.
2. What’s the difference between hiring a security professional vs. engaging a managed security services provider (MSSP)?
Hiring gives you dedicated teams, embedded professionals who are part of your organization, understand your specific environment deeply, and develop institutional knowledge over time. MSSPs provide tooling, monitoring, and response capabilities but rarely have the context to make nuanced security decisions specific to your architecture. Most mature security programs end up with both: an internal team for strategic security ownership and an MSSP for 24/7 monitoring and tier-1 incident handling.
3. Which Indian cities have the best cybersecurity talent pools?
Bangalore leads for cloud security engineering and security architecture. Hyderabad has deep strength in enterprise security, GRC, and compliance roles. Pune is strong for application security and penetration testing. Chennai has growing capacity in security analytics and SIEM operations. For GCC setups, Bangalore and Hyderabad offer the deepest talent pools and the best career infrastructure for retaining senior security professionals.
4. What certifications should I require for different security roles?
Penetration testers: OSCP is the gold standard for hands-on capability; CEH is acceptable but less rigorous. Cloud security engineers: AWS Security Specialty or CCSP depending on environment. Security architects: CISSP or CISM for framework knowledge; evaluate architecture capability separately through practical assessment. GRC specialists: ISO 27001 Lead Implementer, CISA, or CRISC depending on the compliance framework you operate under. SOC analysts: CompTIA Security+, CySA+, or GCIA for threat detection focus. Note: certifications are filters, not evaluations — always assess practical capability independently.
5. How do I retain cybersecurity professionals hired in India?
The two primary attrition drivers for security professionals in India are: lack of challenging technical work (professionals leave when they feel they’re doing repetitive, low-complexity work) and limited visibility into career progression. Retention best practices: give professionals access to meaningful security challenges early, create a defined senior IC or management track, budget for ongoing certification and conference attendance (₹50,000–₹150,000 per person annually is the right range), and ensure your US/EU-based security leadership directly engages with the India team — not just through a middleman.
6. What does it cost to set up a GCC security team in India?
A 5-person GCC security team — security lead, cloud security engineer, AppSec specialist, SOC analyst, and GRC lead — will cost ₹2.5–4.5 crore annually in total compensation depending on seniority and city. Add 25–30% for benefits, compliance, office space, and tooling. Setup costs (recruitment, background verification, equipment, onboarding) run ₹15–30 lakhs as a one-time expense. Expect full operational capability 16–20 weeks from the decision to hire the first person.
7. Can Indian cybersecurity professionals get security clearances for US government work?
Indian nationals cannot obtain US security clearances (Secret, Top Secret, TS/SCI). If your work involves cleared environments or classified data, this is a firm constraint. However, the vast majority of commercial cybersecurity work — including work for US-based fintech, healthcare, enterprise SaaS, and e-commerce companies — does not require security clearances. Data residency and access controls can be structured to comply with applicable regulations without requiring security clearances.
8. What’s the best engagement model for a startup vs. enterprise when hiring security talent from India?
Early-stage startups (seed to Series B): Staff augmentation or a fractional security lead makes more sense than full-time security hires until the security scope justifies it. Budget ₹50,000–₹1,50,000/month for a fractional security advisor or part-time AppSec engineer embedded in your development team. Series C and beyond or regulated industries: Building a dedicated security function makes both operational and compliance sense. Start with a security lead hire, then build the team around their roadmap. Enterprises and GCCs: Dedicated team model with managed hiring and employment infrastructure. The economies of scale justify it at teams of 5+.
If You’re Evaluating This Decision Right Now
If you’re at the point where you’re serious about building a cybersecurity function in India — whether that’s one senior hire or a GCC security team — the most valuable thing you can do before you engage a recruiter or staffing partner is spend 60 minutes clarifying three things: what security problems you’re actually trying to solve in the next 12 months, what your timeline pressure looks like, and what your internal management bandwidth is for a distributed security team.
I’m usually the one on those calls. If you want to talk through the hiring approach before you commit to anything, reach me at mayank@supersourcing.com.
Mayank Pratap is the Co-founder of Supersourcing, an AI-powered hiring and IT services company. He has spent 14 years building technology products and teams, and has led security hiring engagements for fintech platforms, enterprise digital transformation programs, and GCC setups across India. Supersourcing is a vendor partner with Wipro, Virtusa, and Impetus.
 The Three Hiring Models — What Each Actually Costs
The Three Hiring Models — What Each Actually Costs What a Real Security Hiring Process Looks Like (Week by Week)
What a Real Security Hiring Process Looks Like (Week by Week) What Most People Get Wrong About Indian Cybersecurity Salaries
What Most People Get Wrong About Indian Cybersecurity Salaries